Oktane is Okta's annual customer conference. It's also when Okta likes to dump a LOT of product announcements, so I like to follow along. This year Oktane20 went fully virtual, and could be joined for free – anyone can watch the videos.
Here's a pic of their virtual conference lobby that I sat in, waiting on the CEO keynote to start.
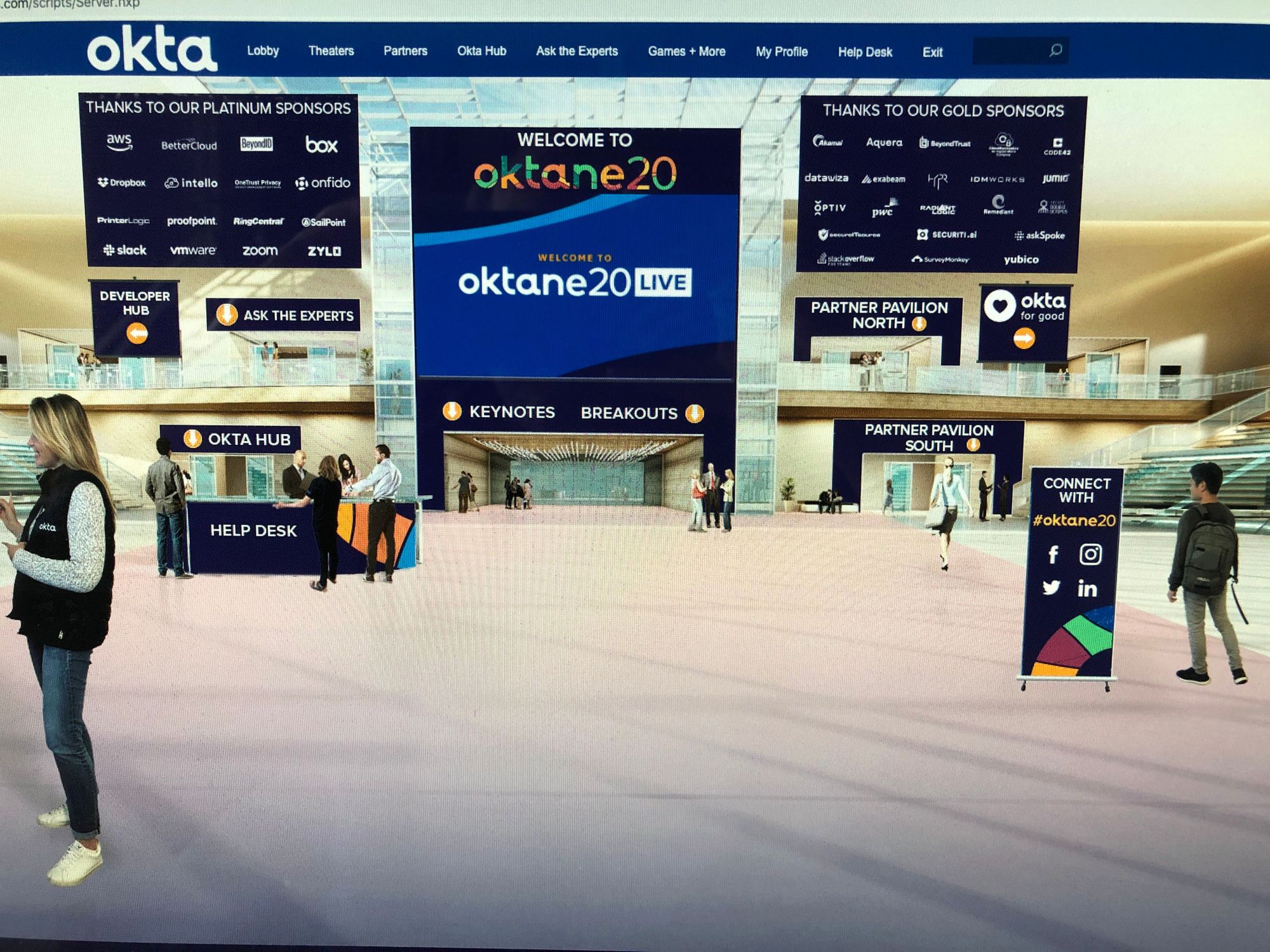
In the partner pavilion, with virtual booths, are companies like Zoom, Dropbox, Yubico, VMWare, RingCentral, Slack, SurveyMonkey, & Box.
But first, some new announcements from earlier in the day.
New Announcements
In addition to Oktane20, Okta scheduled an investor day earlier in the day. A few press releases dropped before the conference started.
Okta Platform Services
Like Twilio has been doing (and Okta started doing last year), they are opening up their platform as building blocks for API integration for partners and customers. This further situates Okta to be able to embed deeply into customers workflows.
By building Okta Platform Services with a modular, service-oriented architecture, Okta, along with its customers and partners, can quickly create new features to speed innovation for everyone in the ecosystem.

Platform blocks:
- Identity Engine (their core contextual Auth engine)
- Directories (user mgmt)
- Integrations (integrating with partners, aka SaaS apps)
- Insights (ML/AI engine over it all)
- Workflows (no-code environment for building complex identity-based enterprise workflows)
- Devices (device mgmt)
Okta Fastpass
New product announced to make an easy-to-use password-less login technique.
- password-less login across devices, apps and OSes
- includes iOS, iPadOS, macOS, Android, and Windows
- use Okta Verify app to register device
- once device is registered, employees can access their apps on any device without ever needing to enter a password
- available Early Access late this year
Once end users register their device via the Okta Verify application, a strong binding is created in the Okta Identity Cloud between the user and the device. When accessing an Okta-managed application via a browser, desktop application, or a native mobile application, end users are not prompted for a password. This means users get an end-to-end password-less login experience when using devices that support biometrics, from unlocking the device, to registering the device to Okta with no password prompt, to subsequent logins on the same device. Optionally, administrators can create fine-grained policies that combine Okta Device Trust, endpoint security integrations, and other adaptive policies with Okta FastPass to deliver secure, password-less experiences for only managed, compliant devices.
Cybersecurity Partnerships
Okta now has deep partnership with EPP providers like CrowdStrike, VMWare/CarbonBlack, and Tanium.
- strengthened partnerships with leading EPP providers (aka the software protecting the DEVICE from malware)
- helps provide deeper contextual security back to Okta products (aka the ML/AI features for advanced security)
- ties into Okta Verify app on device
Relying on the Okta Devices Platform Service, the Okta Identity Cloud is able to ingest those device risk signals to create a comprehensive risk profile of an individual login attempt. Okta can now make access decisions based on security posture signals from an individual’s device, using data delivered by both Okta Verify and leading endpoint management and endpoint detection and response partners. Together with partners, Okta can determine if the operating system is up-to-date, whether or not the device is jailbroken, if the device contains any malware, if the device is managed by IT, and whether or not a firewall is disabled. Okta can then leverage these signals to make the appropriate contextual response to an access request, such as denying access or prompting for an additional factor.
Partner Connect
Okta is upgrading the Partner Connect program.
- improved Partner Accreditation program
- free technical training for partners
- newly launched Okta Innovation Center
- marketing tools for partners
Oktane20
Conference started late - most of it was obviously pre-recorded, especially the interviews. Here are a few quick notes.
Welcome Keynote, Day 1: The Power of Identity
CEO Todd McKinnon kicked off the conference with a preview of how Work From Home is affecting everyone's lives, and a walk through the new announcements from Okta.
Identity is the Core
Line between being a tech company and not a tech company is blurred - we are all tech companies now. Most companies use a 1) collaboration platform, 2) cust data platform, 3) infrastructure platform, 4) HR platform, and 5) finance platform.
Identity platform then needed to tie them all together, so is most important choice. During Work From Home era, identity is the centralizing force for worker mgmt. Irony is that as Okta gets more successful, identity becomes less visible - user interactions become more transparent as security improves.
Apple at last WWDC debuted new SSO library extension, tying identity to device. Okta is world's only Identity Platform. Customers use Okta for its flexibility, workflow.
The Platform Core
Now the broad platform is called Okta Platform Services. Modular components, build custom solutions faster, extends tech.
Identity Engine:
- core auth services moving into modular system
- Okta Identity Engine (modular apis from last years Oktane19)
- Adv Server Access
- Access Gateway
- taking their time to release it, to get it right and assure no impact
Directories (user mgmt):
- Universal Directory
Integrations (partner network):
- Okta Integration Network (now 6500+ integrations)
Insights:
- ML/AI over it all
Okta Workflows: [NEW]
- adv liftcycle mgmt, provisioning
- tying together:
- Okta Hooks (from last year's Oktane19)
- Azuqua acquisition (Mar 2019)
- getting built into every product across platform
- code-free workflow building tool via "cards" (stages)
- tie into or trigger okta events or partner events
Okta Devices: [NEW]
- policies across all of a user's devices
- new Okta Verify app for iOS, iPadOS, Android, Windows, Mac
- can take context of device into account (managed vs unmanaged device)
- Zero Trust mentality
- full view of all devices
- deeper partnership w/ EPP providers
Okta FastPass: [NEW]
- passwordless auth across all devices
- new product integrated across Directories + Identity Engine + new Devices service
- eliminates need for ActiveDirectory
- sets the stage for next-gen Identity Mgmt
Breakout Sessions
The breakouts categories were interesting as it shows what trends are driving Okta right now. Technical breakouts categories:
- Zero Trust
- Lifecycle
- Cloud Access
- Hybrid IT
- Customer Identity
- Integrations
- Developer
- Future of Identity
- Leadership + Industry
Learn How IT Leaders at Box, Slack, Zoom and Okta are Helping Remote Workers
Session of 4 SaaS providers talking about impacts of the pandemic. It was MC'd by the CIO of Box.
- Zoom workers are already heavily remote - didn't have much adjustment to working life.
- Most companies were ready for this - already had remote work options.
- Stay-at-Home is a great test for the future of work layout.
- Slack had a plan in place for this, but the sheer rapidness of volume increases has surprised them.
- Business culture has had to ramp up quickly.
- Okta feels lucky to be cloud-friendly and remote-friendly, was already work-from-home one day a week.
- Cloud-first and cloud-native is having a lot of success now, but still have physical needs. Seeing increase in break-fix requests (broken devices) due to Stay-at-Home. Hiring hasn't stopped - still have need to on-board new users and get them devices. Device inventory is dwindling.
- Another effect that SaaS providers cannot control: Everyone at home has been filling home bandwidth. E.g. Billy in the next room streaming 4k Netflix is affecting Zoom meeting quality.
- Distractions are high - pets, kids, spouses. Loneliness for single folks is a factor. Seeing a lot of social meetups - Happy Hour Open Mics, virtual WaterCooler, etc. Okta and Zoom empl had a cross-company "best background" competition over Zoom.
- Security threats are still going strong - fake COVID-19 focused malware, phishing attempts. Box has seen significant increase in malware attacks in inbound email.
- Okta is offering Adaptive MFA for free right now. They too are seeing way more phishing attacks.
- Huge focus on integrations helping in this situation. Slack is focused on helping 'war room' situations, chat rooms can launch Zoom meetings from the platform.
- Zoom had a CIO webinar, 96% said they were currently remote, 90% said their company was prepared for remote work. Employees aren't so sure.
- Companies using SaaS integration platforms are doing remote work well.
- May be some Zoom fatigue. Zoom usage has exploded, but Slack for one is stressing to its employees to have more social meetings and less work meetings, and instead rely on other channels. [Of course, this benefits Slack, but seems a very legit point.]
- Companies are starting to allow an employee stipend for ramping up remote work capabilities quickly. Slack both provide employees a base device package, as well as stipend for furniture. Box also giving stipend. Okta is making sure engineers get the same setup at home.
- Best of Breed SaaS companies are rising - those providing crucial business operations.
- Okta tries to have 2 providers for everything for its infrastructure (monitoring, etc). Is going through analysis of what cloud companies might be in trouble just in case. Want to be ready.
- Situation is proving workers can be productive & secure working at home.
- Rules are adapting where they need to (physical signatures needed, in-person signoffs, etc). There will be a new normal after this.
Roadmap: Security
Okta has been advancing Passwordless authentication for a while. A brief history:
- 2012 - Desktop SSO
- 2017 - PIV/Smartcard
- 2018 - Device Trust
- 2019 - Factor Sequencing & WebAuthn
- 2019 - Email Magic Link
New products and focuses are:
ThreatInsight:
- went GA 8mo ago
- 4000 orgs have enabled it so far
- 60% auto block suspicious IPs
- 13M suspicious events detected in Feb 2020
HealthInsight:
- went GA in Jan
- personal security recommendations
- actionable recommendations
- dynamically updated
Okta's focus in upcoming Identity Engine release (Q4 2020) is:
Simplify Policy Mgmt:
- share policies between SaaS apps
- step-up auth requirements (eg use MFA) on critical sensitive data apps (instead of all or none)
- Okta FastPass
- registers devices with a specific user
- checks context (network used, etc)
- can step-up auth requirements (eg use MFA) for use identified as high-rish
- Authentication Assurance
- next evolution in Factor Sequencing
- set security outcomes desired
- can set diff policy for diff user classes or app classes (sensitivity, contractors allowed, etc)
- requirements can be based on login context
- allows passwordless auth
- define multiple factors
Example: You can set FastPass passwordless policy on non-sensitive apps (team communications), but require Adaptive MFA on sensitive apps (HR, finances).
Improve Threat Detection:
-
Threats are ever changing
-
Even with MFA, can be bypassed by user, or getting hit by phishing attempt
-
Compromised devices
-
Allowing custom MFA
-
Adopting FIDO2 - all browsers now support
-
more devices embedding FIDO2 capabilities
-
Risk Engine: Risk-based Auth for Okta Verify
- can prompt user to verify auth attempts in Verify app
-
ThreatInsight moving past bad-actor identification via IP
-
Preventing unofficial email clients
Increase end-User self service:
- Focus on lowering help-desk requests
- End users can now see recent sign-ins, and security events like account changes
- Redesigning entire End User settings UI, can access from any device
- Exposing it via API, enterprise can wrap their own end-user settings app.
- Providing more flexible account manage.
- Can recover factors using other factors, instead of requiring IT support. (As opposed to the "security question" method.)
- Allowing enrolling Verify factors on multiple devices (Apple Watch, phone, MacBook TouchID).
Morning Keynote, Day 2: The Value of Identity
COO Frederic Kerrest kicked off day 2 keynote, with a wide ranging discussion with multiple business leaders. This session writeup is interesting reading it now again after the COO's recent TMF interview. He talked about consumer-facing (ever so slightly) in that interview, and it was the whole start of this earlier talk. Makes me wonder what Okta is up to.
Consumer Identity
Consumer identities getting built. "Identity Tax Report" is a new report coming from Okta soon on their studies on CONSUMER side of identity. 52% of consumers don't think search history is tracked. 93% of consumers don't want their identity sold. 1/6 of US doesn't register to vote due to difficulty in process.
Could build digital cloud services that are built around identity. Can make platforms to track all land/house transactions (basically describing what Docusign is doing with their Agreement Cloud).
National identity is scattered should be unified. SSN has become defacto ID. However basing ID on 9 digit SSN is highly insecure & has lead to ~9M US Americans having identity stolen per year. National digital ID going to come. Nation-states have been exploiting these weaknesses in citizen tracking. Russia has been digitally attacking democracies Ukraine, Germany, USofA during voting periods.
Digital identity can help secure our country. Online voting could be built around this identity. Okta is working heavily with political parties at fed/state/local level to help secure them.
[RED ALERT - future pivot being spotted, a move into consumer-facing side that could easily be built over their enterprise platform's core capabilities.]
Move to Cloud
Still early innings...
- IT spent >3.9T/yr. Enterprise software 507B
- SaaS is 116B, 25%, 3% of overall
- Global movement
- Brazil making huge investments
- India cloud set to triple
- China cloud
- est 60% of fed depts using cloud in 3yrs
Tyson Foods CTO then spoke on moving 85yr old company to modern infrastructure. I posted this part earlier in a separate post on how analytics seem a very valuable service right now, after seeing how Tyson CTO was heavily using analytics to be a lot more nimble during this pandemic.
Software is Eating the World
Companies are still moving towards being SaaS tool driven.
VP of HP GreenLake Central (Hybrid Cloud) was interviewed. Every company is a technology company. Businesses cannot operate without tech. HP has a new cloud platform, GreenLake, that came out Dec'19 in preview, and now have 1000 customers on it. Bridges cloud scale & managed services with on-prem security. HP moving all services to this new platform by 2022 (3yr timeline). Should GA soon.
GreenLake uses Okta for customer identity mgmt. HP wanted help solving the Identity program and wanted it to be cloud-forward. Leverages Okta to handle that, so their engineers can focus on HP's core focus. Time-to-live was super fast - Aug/Sept was initial release, then Okta got put in place for onboarding customers by Nov.
Identity is a critical aspect for customer's user experience. Hybrid cloud is very complex. Okta is now deeply embedded via APIs/SDKs. Will continue to leverage the new API/modular design coming from Okta Platform Services.
[So let's be clear, HP's entire cloud-native future services platform is based on Okta for Customer Identity & auth. Same as Adobe did for Adobe Creative Cloud.]
Traditional Perimeter is Gone (Zero Trust)
Reduce risk by verifying users at all time. You must assure RIGHT people have RIGHT level of access to the RIGHT resources in the RIGHT context, and that the context is continually accessed. This is ZERO TRUST paradigm (see my Flavors of Security posts if you aren't up on this).
Okta surveyed 500 companies. In North America, last year only 16% of companies were planning Zero Trust. Today now 60% have or are planning to add plans in 12-18mo.
CISO from Baker Hughes (energy co) spoke on transforming itself into an energy TECH company. Expanding beyond oil/gas into all energy tech. Has moved into Zero Trust for maintaining their entire global workforce.
June of 2017 was a merger between 2 large companies each with 35k global empls. Had to build all new business operations, so was opportunity to pivot to Zero Trust. It's been 3yr transition into new security paradigm. Controlling access to new critical software apps for tracking finance, assets, intellectual property, employees. Massive Office365 deployment. Global employees between office & in-field staff.
Nation-states hackers are working together. High level of security is critical.
Interesting stuff, with the Day 2 Keynote as the most interesting of the presentations. You can watch any of these sessions yourself!
- muji
